One Exploit to Rule them All? On the Security of Drop-in Replacement and Counterfeit Microcontrollers
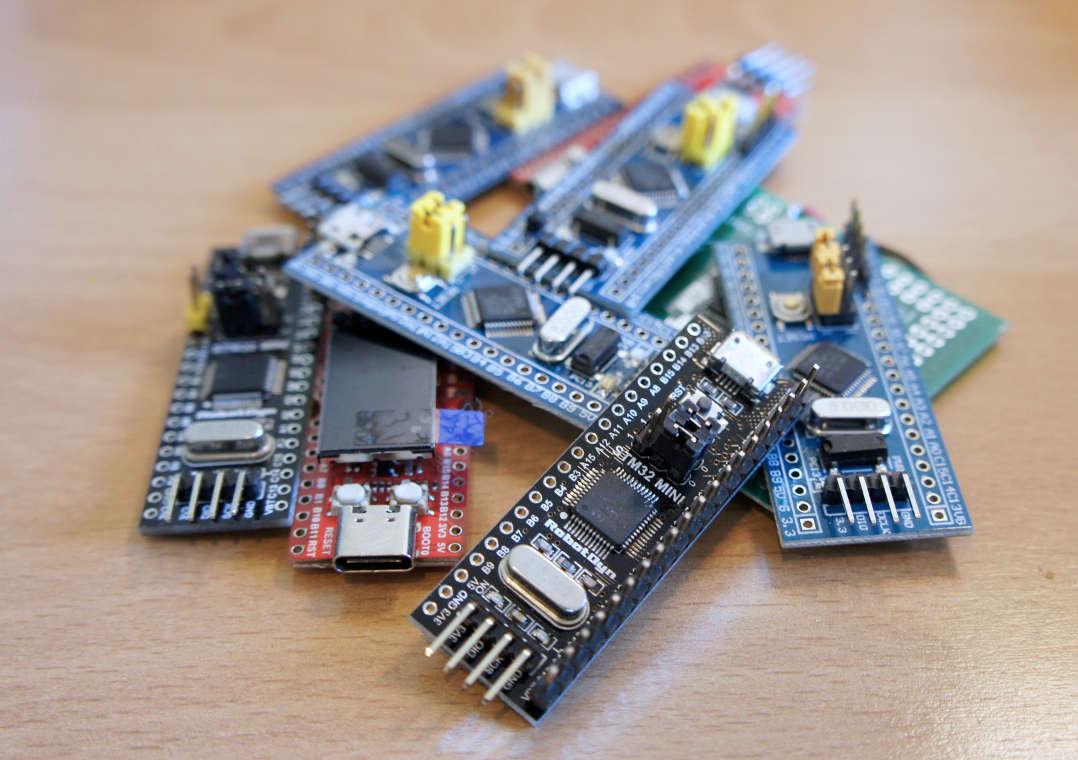
After Exception(al) Failure, we bought a bunch of drop-in replacement chips for the STM32F1 series and analyzed them with respect to their firmware security features. We found lots of severe vulnerabilities and even encountered counterfeited devices. The results of this research will be published in form of a scientific paper at the 14th USENIX Workshop on Offensive Technologies on 11 August 2020. The work is a joint collaboration of Johannes Obermaier, Marc Schink and Kosma Moczek.
We will not publish the paper in advance to the conference in order to adhere the deadline of the coordinated disclosure process. However, here is a short teaser to bridge the time gap until the publication:
With the increasing complexity of embedded systems, the firmware has become a valuable asset. At the same time, pressure for cost reductions in hardware is imminent. These two aspects are united at the heart of the device, i.e., the microcontroller. It runs and protects its firmware, but simultaneously has to prevail against cheaper alternatives. For the very popular STM32F1 microcontroller series, this has caused the emergence of many competitors in the last few years who offer drop-in replacements or even sell counterfeit devices at a fraction of the original price. Thus, the question emerges whether the replacements are silicon-level clones and, if not, whether they provide better, equal, or less security. In this paper, we analyze a total of six devices by four manufacturers, including the original device, in depth. Via a low-level analysis, we identify all of them as being individually developed devices. We further put the focus on debug and hardware security, discovering several novel vulnerabilities in all devices, causing the exposure of the entire firmware. All of the presented vulnerabilities, including invasive ones, are on a Do it Yourself (DiY) level without the demand for a sophisticated lab – thereby underlining the urgency for hardware fixes. To facilitate further research, reproduction, and testing of other devices, we provide a comprehensive description of all vulnerabilities in this paper and code for proofs-of-concepts online.
More information will be published here soon – stay tuned!
Update (11 August 2020): The paper and supplementary material are now available.