Unlock the Door to my Secrets, but don't Forget to Glitch @ CCCamp23
In Security and Trust in Open Source Security Tokens, we presented an attack vector that exploits a feature which allows to disable the debug interface protection of a microcontroller under the condition that its entire flash memory is erased first. With the help of fault injection, the erase operation can be suppressed which ultimately allows access to the entire flash memory. Our publication left many open questions such as the practicability and generalizability of this attack vector. To answer these questions, we conducted a comprehensive evaluation in form of an academic research paper which includes multiple microcontrollers and different fault injection techniques.
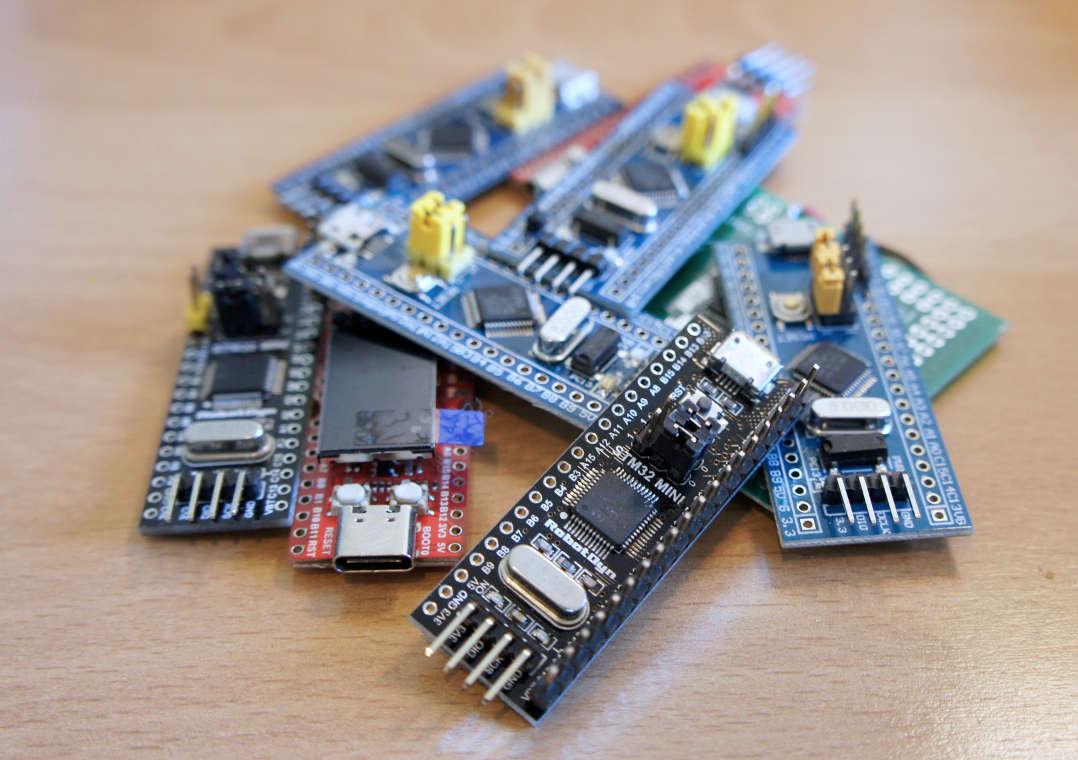
Since publishing research papers is tedious and takes a lot of time, we decided to present a small preview of our results on the Chaos Communication Camp 2023. The talk gives a short introduction to the so-called flash erase suppression attack vector together with a live demonstration on the STM32L422 microcontroller. We chose this device for two reasons. First, it is already known to be vulnerable (CVE-2021-29414) due to our first publication and thus not part of the current coordinated vulnerability disclosure (CVD) process. Second, the voltage glitching setup for this microcontroller is very handy and thus predestined to be shown live on stage. Unfortunately, I was unable to attend the camp at short notice. Thankfully my colleague Silvan Streit was also at the camp and offered to give the talk for me. The video recording is available on media.ccc.de and the slides can be found here.
The comprehensive analysis will be presented at the Cryptographic Hardware and Embedded Systems (CHES) 2024 conference. I will cover the paper in a separate blog post and provide additional details and material, so stay tuned.